Summary
Within SCCM’s client push installation properties, there exists a setting to “Allow connection fallback to NTLM.” This setting allows the site server to fallback to NTLM if Kerberos fails (Figure 1).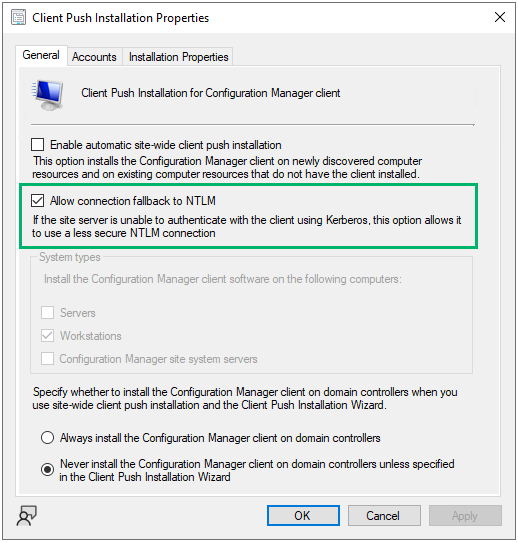
Linked Defensive IDs
- PREVENT-1: Patch site server with KB15599094
- PREVENT-5: Disable automatic side-wide client push installation
Associated Offensive IDs
- ELEVATE-2: NTLM relay via automatic client push installation
- ELEVATE-3: NTLM relay via automatic client push installation and AD System Discovery
References
- Chris Thompson, Coercing NTLM Authentication from SCCM